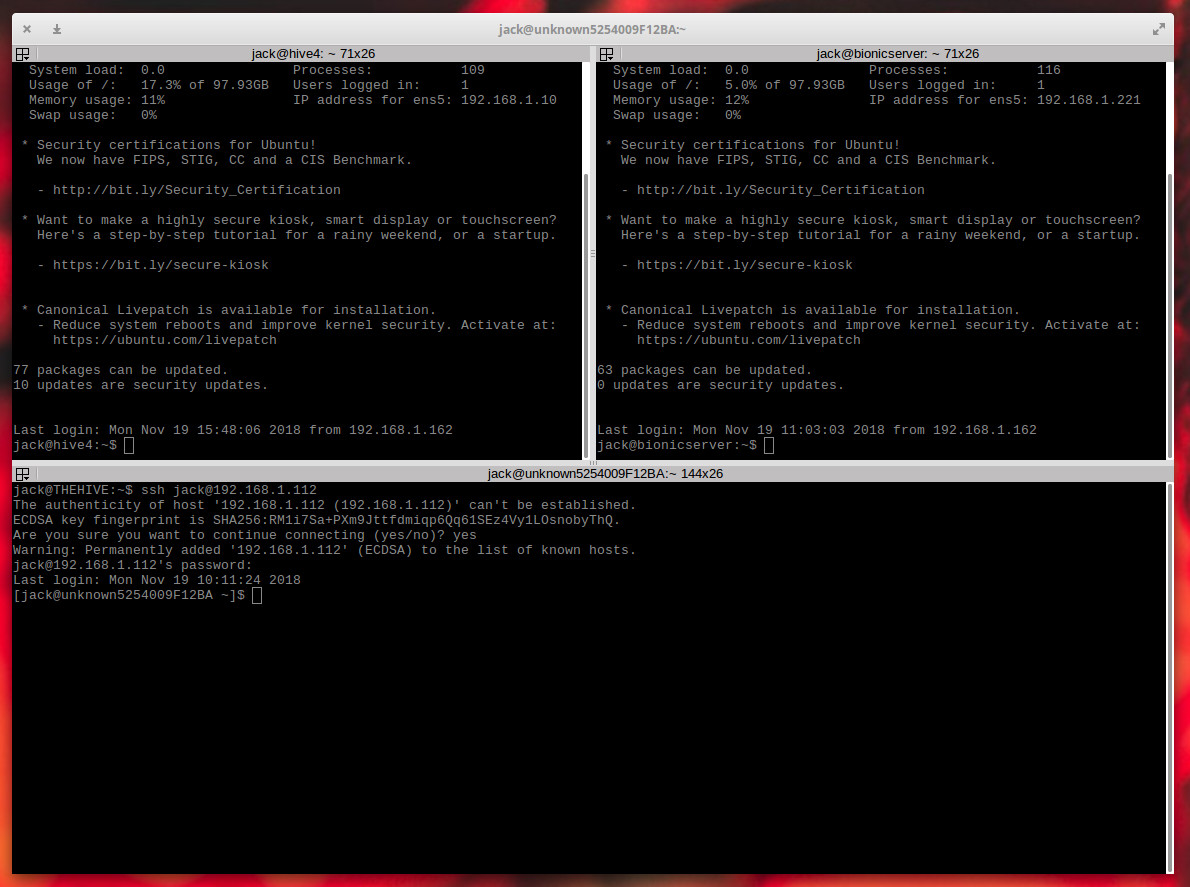
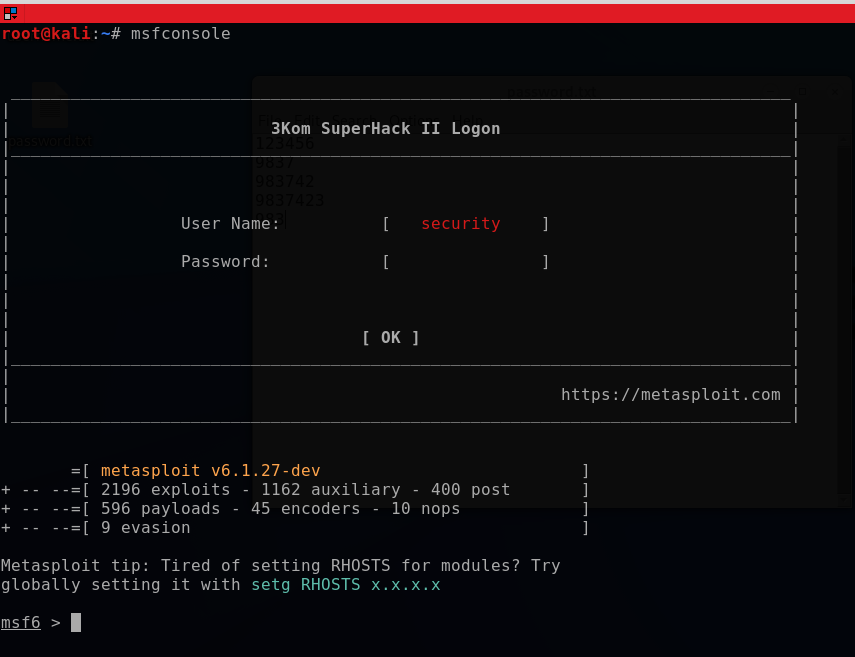
Incident Response Case: From SSH Tunnel To Endpoint Analysis | by Alparslan Akyıldız academy | Medium
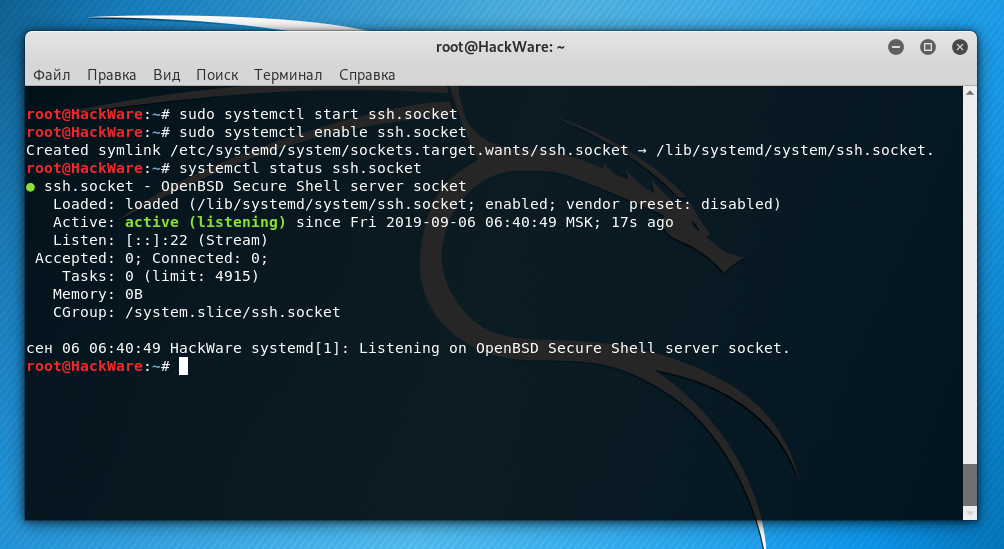
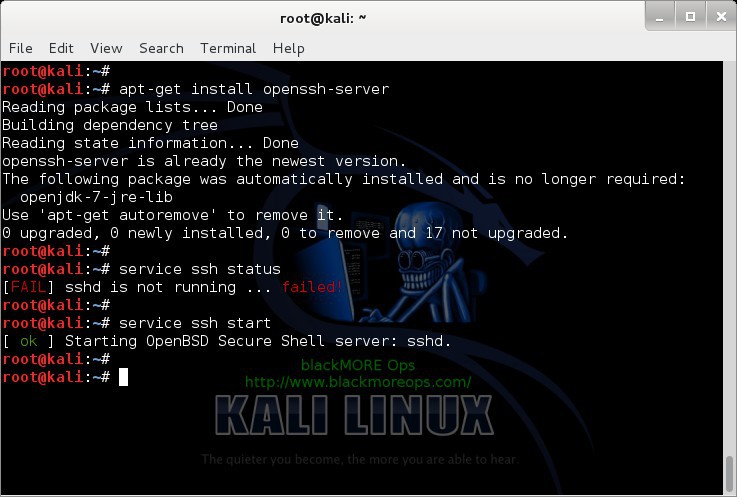
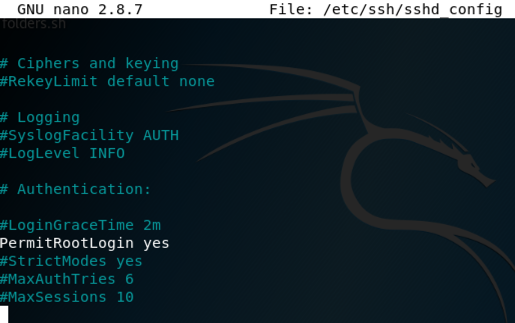
How to enable SSH in Kali Linux. How to connect to Kali Linux via SSH - Ethical hacking and penetration testing
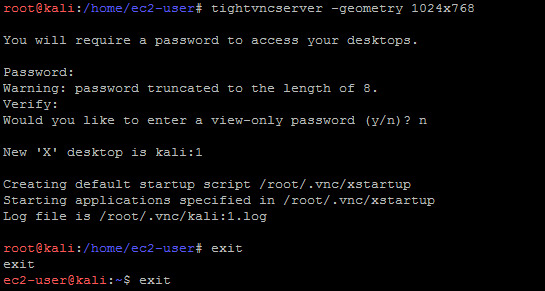
![Enabling root and password authentication on SSH - Hands-On AWS Penetration Testing with Kali Linux [Book] Enabling root and password authentication on SSH - Hands-On AWS Penetration Testing with Kali Linux [Book]](https://www.oreilly.com/api/v2/epubs/9781789136722/files/assets/869ede0f-4bfe-48c6-99c1-0628a7037da2.png)
Enabling root and password authentication on SSH - Hands-On AWS Penetration Testing with Kali Linux [Book]